CHERRY SECURE BOARD 1.0
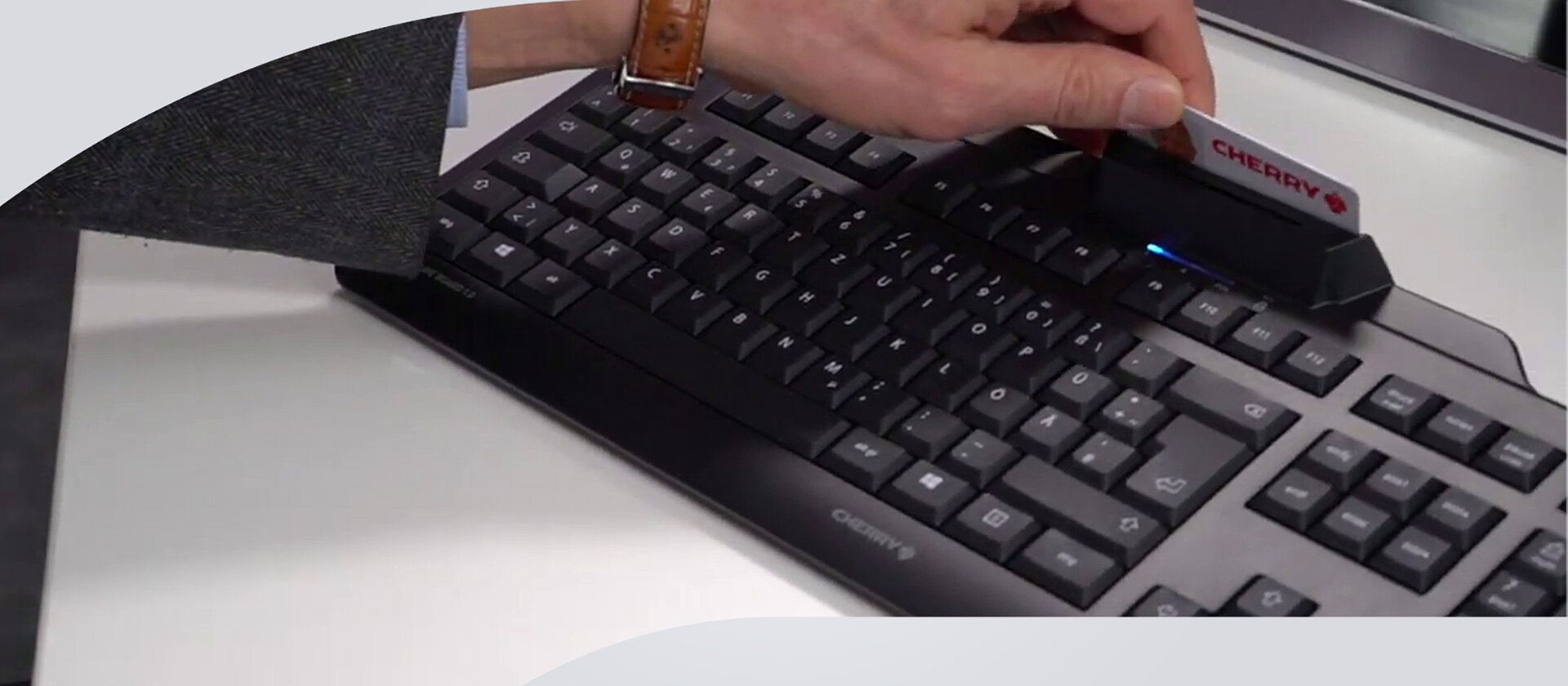
The CHERRY SECURE BOARD 1.0 is an ergonomic keyboard with an integrated reader for smart cards and cards/tags with an RF/NFC interface. For added security and confidentiality, the keyboard can be switched to a secure mode. Now the device can authenticate itself with a certificate and the key transmission is encrypted. This renders hardware key loggers useless and because the standard keyboard channel is locked, BadUSB attacks cannot be carried out on it. Thin clients that have the necessary software integrated are particularly suitable for using these functions.
Highlights
- Intelligent security keyboard with integrated reader for smart cards and cards/tags with RFID/NFC interface
- Secure mode with authentication and encryption, especially with thin clients
- PC/SC smart card reader, CCID compatible
- Protocols: T=0, T=1, T=CL
- Read/write with ISO 7816 and ISO 14443 A/B compliant cards
- Flat design, low smart card contacting unit
- Satisfies FIPS-201 requirements
- DE version with DIN/GS compliant layout and meets with BGI-650 ergonomics guide
- Standard for Windows and Linux
- One-handed operation of smart card module
- Awarded the “Blauer Engel” environmental seal


CHERRY SECURE BOARD 1.0
A central component of modern security concepts is the authentication of users and the authorization of access. Passwords have long since ceased to provide comprehensive access protection - they are all too easily forgotten, changed too infrequently or inadvertently disclosed to third parties due to carelessness.
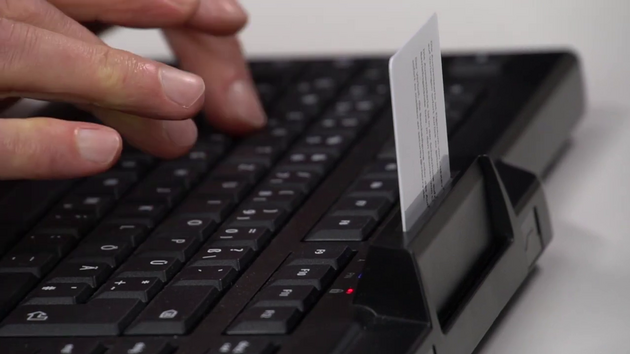
State of the art, especially in highly sensitive areas, is often two-factor authentication using a smart card. CHERRY follows the “make two into one” approach here and offers a space-saving alternative with the KC 1000 SC and the SECURE BOARD 1.0, in which the card reader is integrated into the keyboard.
In addition, the SECURE BOARD 1.0 also has a contactless card reader located at the back of the keypad. This can also conveniently read RFID and NFC cards or tags contactless This equipment opens up a whole range of applications for the SECURE BOARD 1.0: ID card systems for closed user groups can be used via the keypad and company ID cards, for example, can be read.
Security starts with the input device
We live in a digital world in which everyone is increasingly connected to everything - companies, authorities, institutions with citizens, partners, suppliers and customers. A fundamental element of any security strategy is controlling who has access to the respective IT infrastructure. Cyber security is still often seen as a software problem and assumes that endpoints for trusted applications are secure. However, input devices can also be gateways through which sensitive data input can be tapped before further security measures such as firewalls or virus scanners even take effect. Security keyboards such as the SECURE BOARD 1.0 from CHERRY provide a remedy here.
Insider attacks as one of the greatest sources of danger
Sviluppi come la digitalizzazione e i big data e le montagne di dati in crescita esponenziale che ne derivano stanno suscitando desideri. Non solo da cyber criminali attaccando dall'esterno dell'azienda, ma anche da dipendenti malintenzionati o visitatori esterni - insider che sono dopo informazioni dai loro datori di lavoro, clienti, partner e agenzie governative.
La maggior parte delle violazioni dei dati sono commesse da insider.
Secondo il "2024 Data Breach Investigations Report" di Verizon, gli insider sono responsabili del 70% degli incidenti nel settore sanitario e del 59% nel settore pubblico. Queste violazioni hanno coinvolto qualcuno che entrava dall'interno dell'organizzazione. Scoprite come i prodotti CHERRY vi aiutano a risolvere la violazione della sicurezza!
In passato, il rischio insider consisteva in documenti cartacei, per esempio, che lasciavano l'azienda inosservata e senza autorizzazione. Oggi, il rischio è molte volte superiore - i dati digitali, la risorsa più preziosa in qualsiasi azienda, spesso si inserisce su una chiavetta USB o può essere rimosso direttamente dalla società. In molti casi, le imprese affrontano il problema solo dal lato del software. Ad esempio, i sistemi di prevenzione e di protezione contro le intrusioni dovrebbero contribuire a rilevare e analizzare gli attacchi dall'interno in una fase precoce. In molti casi, la sicurezza inizia dal dispositivo di input.

The human factor: closing the gateway from the inside
Like the environment, the equipment should also be protected according to the security requirements. Possible threats include theft, sabotage, internal hacking or unauthorized access. Cyber criminals - whether malicious employees or external attackers - like to use keyloggers or BadUSB devices for this purpose. Sensitive data, passwords or access codes are tapped by manipulating the input device. This form of sabotage can be prevented comparatively simply but very effectively with the SECURE BOARD 1.0 from CHERRY. With the integrated secure mode, proof of authenticity of the device is certificate-based and key transmission is encrypted. This makes it impossible for hardware keyloggers to intercept sensitive access data and passwords. By blocking the standard keyboard channel, “BadUSB” attacks are also a thing of the past: USB sticks that log on to the system as a keyboard cannot inject uncontrolled input and malicious code.
Defense against malicious code from BadUSB devices
They are small, fit in trouser pockets and the palm of your hand and can transport huge amounts of data: USB sticks. If these mobile data carriers are used for data theft or other malicious actions, the USB sticks, which are neutral in themselves, quickly become a bad USB device.
The problem is that each USB stick has its own controller and firmware in an area that is not visible to the normal user or the operating system. This means that manipulations cannot be detected. For example, the firmware of USB controllers and therefore the BIOS of USB devices can be read and changed. The communication of the USB controller with the host system is completely controlled here.

The manipulated firmware can then turn the USB stick into a network card or a keyboard and redirect or manipulate data traffic, or even inject malicious code into the computer. Unfortunately, existing USB devices can also be reprogrammed in this way and thus subsequently compromised.
The SECURE BOARD from CHERRY provides a remedy here: when the keyboard's secure mode is activated, the standard keyboard channel is blocked. This makes “bad USB” attacks a thing of the past. USB sticks that log on to the system as a keyboard cannot inject any uncontrolled input or malicious code. Well-known thin client manufacturers (e.g. IGEL) already support the use of secure mode and have integrated the necessary software for this. A corresponding solution for Windows will be available soon.
Protect sensitive data (passwords, emails) from hardware keyloggers
A keylogger is a piece of hardware or software that is used to log the user's entries on a computer keyboard and thus monitor or reconstruct them. Keyloggers are used, for example, by crackers, intelligence services or investigative authorities to obtain confidential data such as passwords or PINs. A keylogger can either record all entries or wait for specific keywords, such as access codes, and only then record them in order to save storage space.
Hardware keyloggers are plugged directly between the keyboard and the computer and can therefore be installed within seconds. Devices that store the spied-out data in an integrated memory (RAM, EPROM, etc.) are then removed again later. The entries logged by them are then read out on another computer. Other techniques send the logged data via networks or wirelessly.
How the CHERRY SECURE BOARD 1.0 protects sensitive data
With the SECURE BOARD 1.0, CHERRY has a solution in its portfolio that effectively eliminates precisely these threats posed by hardware keyloggers: With the secure mode, the device's proof of authenticity is certificate-based and key transmission is encrypted. This makes it impossible for hardware keyloggers to intercept sensitive access data and passwords.
The CHERRY SECURE BOARD 1.0 offers first-class security features and reliable performance, ideal for use in sensitive and demanding work environments.
Further chip card-based applications and advantages of the dual-interface feature can be found here:
Properties
| Warranty | 2 years warranty |
|---|---|
| Software support | CHERRY KEYS, PC/SC Diagnose Tool |
| Cable length | 5.91 ft |
| Keycap material | ABS |
| Key labeling | Laser etching |
| Special key functions | Calculator, e-mail program, Browser, PC lock |
| Adjustable feet | integrated |
| Status LEDs | in housing |
| Key technology | Rubberdome |
| Total Key Travel | 3 mm |
| Pre-Travel | 2,5 mm |
| Actuating force (cN) | 70 cN |
| Service life per key (in million strokes) | 10 mio. actuations |
| Switching characteristics | standard |
| Keyboard format | Full-size (100%) |
| Integrated metal plate | yes |
| N-Key Rollover | no |
| Anti-ghosting | no |
| Key encryption | Cha Cha 20 |
| Response time | 3-5 ms |
| Internal memory | no |
| Chip card types | ISO 7816 Cards, ISO 14443A Cards, ISO 14443B Cards, ISO 15693 Cards |
| Operating system | Linux, Mac OS, Windows Vista (64Bit), Windows XP, Windows XP (64Bit), Windows 7, Windows 8, Windows 10, Windows 11 |
| System Requirements-Hardware | USB-A |
| Cable length | 5.91 ft |
| Length of product without packaging | 18,03 in |
| Width of product without packaging | 7,4 in |
| Height of product without packaging | 1,81 in |
| Scope of delivery | Manual, Keyboard |
| Illumination | no |
Scope of delivery
- Manual
- Keyboard
| Article number | Layout | Product colour | ||
|---|---|---|---|---|

|
JK-A0400BE-2 EAN: 4025112090615 |
BE (Belgium) | Black | |

|
JK-A0400CH-2 EAN: 4025112090516 |
CH (Switzerland) | Black | |

|
JK-A0400DE-2 EAN: 4025112090127 |
DE (Germany) | Black | |

|
JK-A0400ES-2 EAN: 4025112090530 |
ES (Spain) | Black | |

|
JK-A0400EU-2 EAN: 4025112090141 |
EU (USA+ €-Symbol) | Black | |

|
JK-A0400FR-2 EAN: 4025112090554 |
FR (France) | Black | |

|
JK-A0400GB-2 EAN: 4025112090578 |
GB (United Kingdom) | Black | |

|
JK-A0400IT-2 EAN: 4025112090592 |
IT (Italy) | Black | |

|
JK-A0400PN-2 EAN: 4025112091421 |
PN (PanNordic) | Black | |

|
JK-A0400BE-0 EAN: 4025112090608 |
BE (Belgium) | Grey | |

|
JK-A0400CH-0 EAN: 4025112090509 |
CH (Switzerland) | Grey | |

|
JK-A0400DE-0 EAN: 4025112090110 |
DE (Germany) | Grey | |

|
JK-A0400ES-0 EAN: 4025112090523 |
ES (Spain) | Grey | |

|
JK-A0400EU-0 EAN: 4025112090134 |
EU (USA+ €-Symbol) | Grey | |

|
JK-A0400FR-0 EAN: 4025112090547 |
FR (France) | Grey | |

|
JK-A0400GB-0 EAN: 4025112090561 |
GB (United Kingdom) | Grey | |

|
JK-A0400IT-0 EAN: 4025112090585 |
IT (Italy) | Grey | |

|
JK-A0400PN-0 EAN: 4025112094958 |
PN (PanNordic) | Grey |